A vital worm present in Google’s legitimate WordPress plugin with 300,000 lively installations may just permit attackers to realize proprietor get admission to to focused websites’ Google Seek Console.
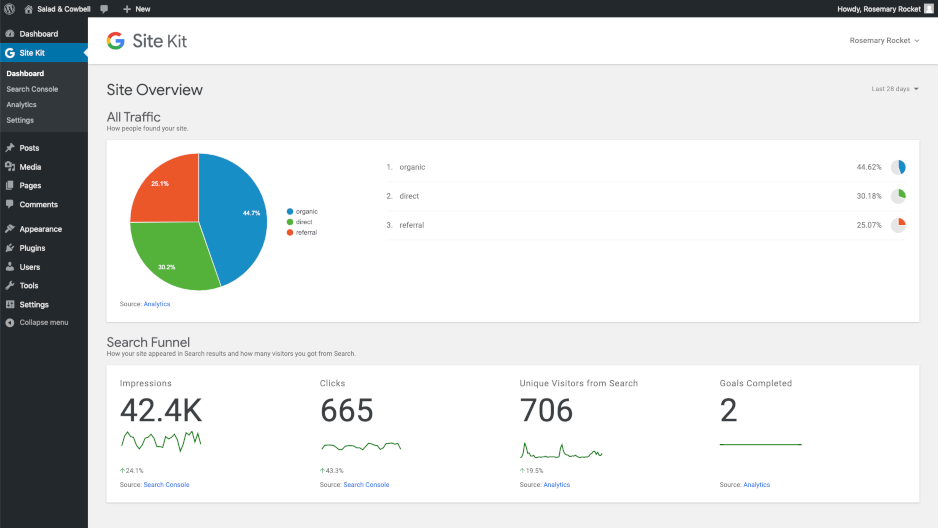
Website Equipment is a WordPress plugin designed through Google to lend a hand website online house owners to realize perception on how their guests use and to find their web page by the use of legitimate stats accumulated from a couple of Google gear and displayed at once within the WordPress dashboard.
The plugin additionally makes it more straightforward to arrange and configure key Google merchandise such because the Seek Console, Analytics, Tag Supervisor, PageSpeed Insights, Optimize, and AdSense.
Privilege escalation vulnerability
The Google Seek Console Privilege Escalation vulnerability used to be came upon through the Wordfence Danger Intelligence crew on April 21 and reported to the Google Safety crew on April 22.
As Wordfence main points, the worm is led to through the disclosure of the proxySetupURL throughout the HTML supply code of admin pages, an URL used to attach the Website Equipment plugin to the Google Seek Console via Google OAuth.
This used to be coupled with every other factor the place “the verification request used to make sure a website online’s possession used to be a registered admin motion” didn’t have any capacity exams taking into account such requests to return from any authenticated WordPress consumer.
“Those two flaws made it imaginable for subscriber-level customers to turn out to be Google Seek Console house owners on any affected website online,” Wordfence explains.
As soon as an attacker would’ve won proprietor get admission to to a website online’s Google Seek Console, they may use it to their merit in a couple of techniques, together with the method to:
• facilitate black hat search engine optimization campaigns through manipulating seek engine outcome pages
• inject malicious code for illicit monetization (when coupled with different exploits)
• take away pages from Google seek engine outcome pages (SERPs)
• alter sitemaps
• view aggressive efficiency information
“Unwarranted Google Seek Console proprietor get admission to on a website online has the possible to harm the visibility of a website online in Google seek effects and affect earnings as an attacker eliminates URLs from seek effects,” Wordfence added.
“Extra in particular, it might be used to help a competitor who desires to harm the score and popularity of a website online to higher enhance their very own popularity and score.”
Mitigation and protection measures
Thankfully, Google will robotically ship notification emails to website online house owners each time new Google Seek Console house owners are added to a website online pronouncing that “Belongings house owners can exchange vital settings that impact how Google Seek interacts along with your website online or app.”
Simply in case that e mail alert would possibly have landed on your e mail account Junk mail folder, Wordfence supplies detailed directions on tips on how to examine the integrity of Google Seek Console possession to test if a rogue proprietor has been added through a malicious attacker and take away them.
As an additional precaution, you’ll additionally reset your WordPress Website Equipment connection so that you’re going to need to reconnect all prior to now attached Google products and services.
Google patched the vulnerability on Would possibly 7 with the discharge of Website Equipment 1.eight.zero, after a patch for the protection flaw used to be made public within the plugin’s Github Repository on Would possibly four.
All Website Equipment customers are instructed to right away replace their set up to the 1.eight.zero model, the most recent to be had absolutely patched model.
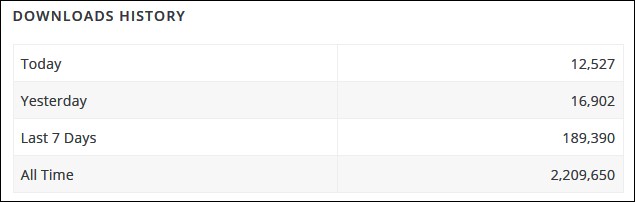
Sadly, whilst virtually 200,000 web page house owners have up to date their Website Equipment plugins because the patch used to be launched virtually every week in the past, over 100,000 websites are nonetheless uncovered to assaults making an attempt to take advantage of this vulnerability.